KYC Fraud Is Increasing Faster Than Most Pipelines Can Handle
Digital banks are scaling onboarding aggressively. Verification throughput is increasing, but so is fraud exposure.
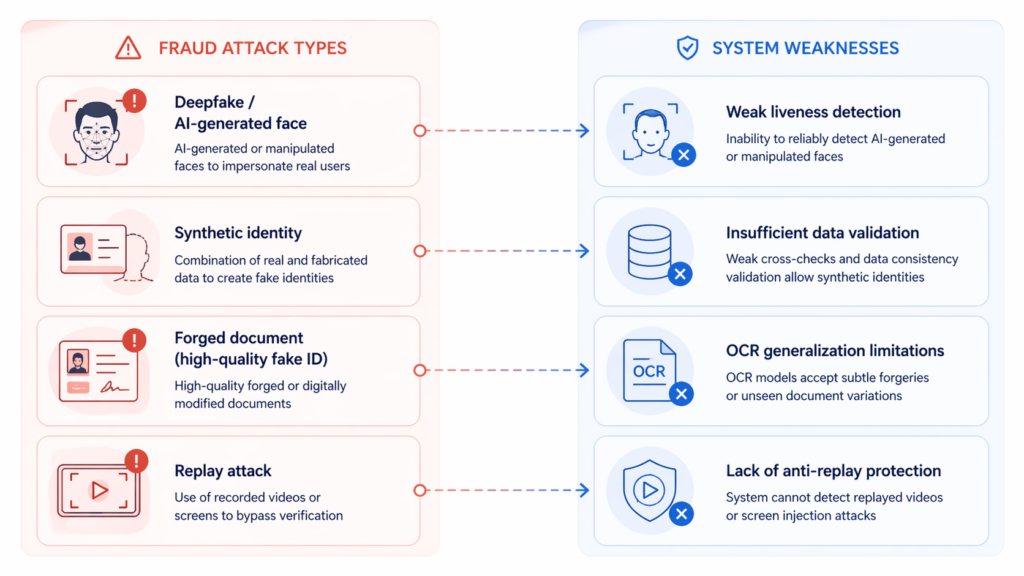
The core issue is not a single model failure. It is a system-level mismatch between legacy KYC pipelines and modern AI-driven attack vectors. Attackers are no longer relying on static artifacts. Instead, they leverage AI-generated faces such as deepfakes and face swaps, combine real and fabricated data to create synthetic identities, and use high-quality document forgeries that can pass OCR validation with high confidence.
Most KYC systems were not designed for this threat model. As a result, false acceptance rates increase without obvious system alerts, creating a form of silent risk accumulation that is difficult to detect in real time.
Root Causes: Where Traditional KYC Pipelines Break Down
Latency Constraints Force Trade-offs
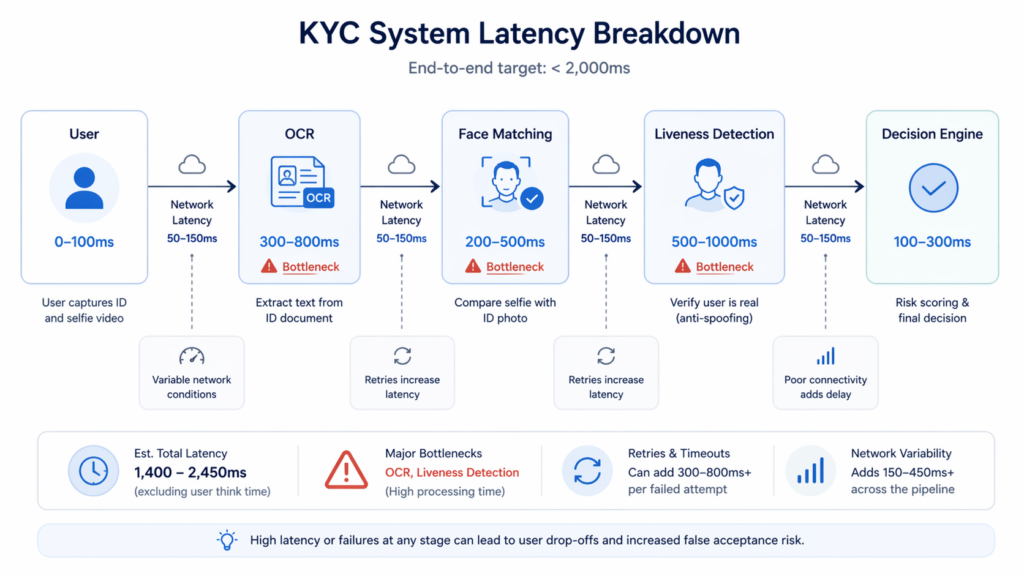
KYC systems typically operate under strict SLA constraints, often requiring end-to-end verification within two seconds. A standard pipeline involves document OCR, face comparison, and liveness detection, each introducing its own latency overhead. Document OCR alone can take several hundred milliseconds, while face comparison and server-side liveness detection further increase total processing time.
Under peak load conditions, systems often compensate by lowering image quality thresholds, skipping secondary validation steps, or reducing retry mechanisms. While these adjustments help maintain throughput, they directly weaken fraud resistance and create exploitable gaps.
Static Models vs. Adaptive Fraud
Traditional KYC systems rely heavily on fixed similarity thresholds and rule-based fraud detection. These approaches assume relatively static attack patterns. However, modern fraud techniques are highly adaptive. Deepfake models can mimic micro-expressions, synthetic identities can pass consistency checks across multiple data points, and replay attacks can bypass basic liveness detection.
This creates a structural failure mode in which model confidence remains high, even as accuracy degrades under adversarial conditions. The system continues to approve fraudulent users while appearing statistically stable.
Network and Payload Inefficiencies
Most KYC pipelines are built on REST APIs using JSON payloads, with image sizes typically ranging from hundreds of kilobytes to several megabytes. Each verification session may require multiple network round trips, making the system highly sensitive to network conditions.
In mobile-first environments, where users rely on unstable connections, packet loss and retransmissions increase latency and degrade user experience. These issues often lead to timeouts or incomplete verification sessions, reducing both conversion rates and system reliability.
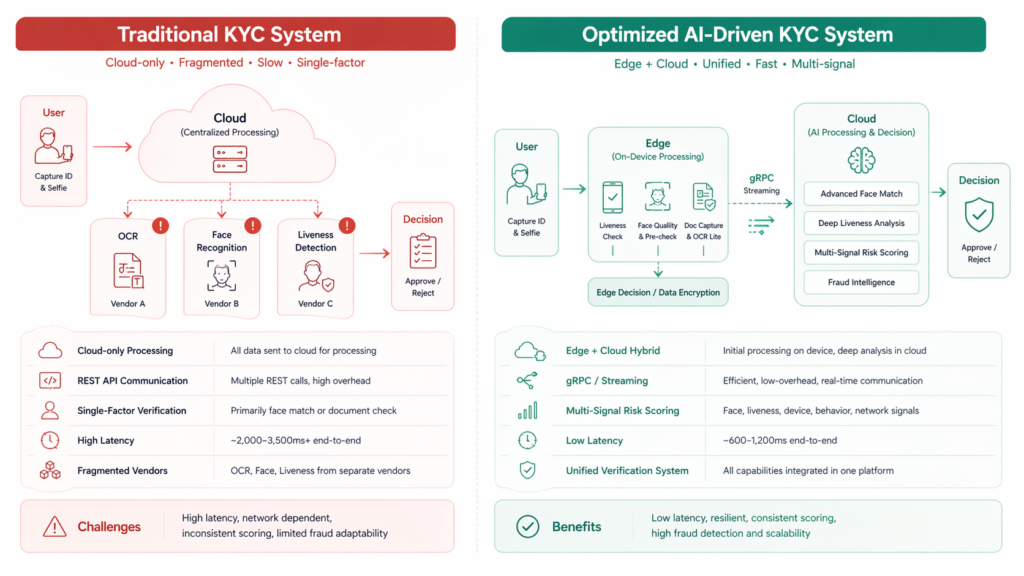
Fragmented Verification Architecture
Many KYC implementations rely on a combination of separate vendors for OCR, face recognition, and liveness detection. While this approach provides flexibility, it introduces significant architectural challenges. Each component operates with its own scoring logic, making it difficult to unify results into a consistent decision framework.
This fragmentation leads to inconsistent outputs, duplicated processing logic, and limited ability to perform cross-signal validation. As a result, fraud patterns that span multiple signals are often missed.
How to Optimize KYC Systems for Fraud Resistance
Step 1: Move Liveness Detection to the Edge
One of the most effective optimizations is shifting initial liveness detection to the client side. By deploying lightweight models directly on mobile devices, systems can perform real-time spoof filtering before data is transmitted to the server.
With model sizes reduced through quantization, on-device inference can run efficiently on standard mobile hardware. This approach reduces server load, filters out low-quality or fraudulent inputs early, and significantly improves response times.
Step 2: Apply Model Quantization
Model optimization plays a critical role in scaling KYC systems. Techniques such as INT8 quantization can reduce model size by up to 70 percent while maintaining near-original accuracy. This reduction improves inference speed, lowers memory consumption, and enables deployment across a wider range of devices.
The result is a more scalable system that can handle higher concurrency without compromising performance.
Step 3: Replace REST with gRPC for High Throughput
While REST APIs are widely used, they introduce unnecessary overhead in high-frequency, real-time scenarios. gRPC, which uses a binary protocol and supports streaming, offers a more efficient alternative.
By reducing payload size and enabling continuous data transfer, gRPC improves latency and system responsiveness under load. For implementation teams, Face++ API Documents can also help developers understand how to integrate verification capabilities into production workflows..
Step 4: Implement Multi-Signal Risk Scoring
Modern fraud detection requires moving beyond single-factor verification. Instead of relying solely on face matching, systems should integrate multiple signals, including liveness confidence, device fingerprinting, and behavioral patterns such as gesture timing and motion consistency.
This multi-signal approach enables dynamic risk scoring, allowing systems to adjust verification thresholds based on context. It reduces false acceptance rates and improves adaptability against evolving fraud techniques.
Compliance and Infrastructure Constraints
Regulatory Requirements
KYC systems must comply with global regulatory standards, including FATF recommendations, which define requirements for customer due diligence and anti-money laundering controls. These regulations require strong protection of biometric data, including encryption during transmission and storage, as well as full auditability of verification processes.
Reference: https://www.fatf-gafi.org/en/publications/Fatfrecommendations/Fatf-recommendations.html
Infrastructure Limitations
In many markets, infrastructure conditions add additional complexity. Network instability remains common, device performance varies widely, and most users rely on mobile-first onboarding flows.
These constraints require systems to be designed for resilience. Practical approaches include implementing offline-capable SDKs, applying adaptive image compression to reduce payload sizes, and adopting edge-first processing strategies to minimize reliance on network stability.
Building an AI-Driven KYC Architecture
A modern KYC system must integrate detection, prevention, and adaptability into a unified architecture.In practice, achieving this level of system integration requires a unified approach rather than assembling multiple standalone components. At Face++, we build our architecture around this principle by combining face recognition, advanced liveness detection, and document verification into a single, cohesive system.
By integrating these capabilities with a multi-signal risk engine, the system can support real-time fraud detection while maintaining low latency and consistent decisioning across different scenarios. This approach reduces reliance on fragmented vendor stacks and improves both system performance and fraud resilience.
This typically involves a hybrid edge and cloud model, where edge devices handle real-time validation while cloud systems perform deeper analysis. Advanced liveness detection models are used to identify deepfake artifacts, reflection inconsistencies, and temporal anomalies across frames.
Security must be enforced across the entire lifecycle, including encryption in transit using TLS 1.3 and secure handling of biometric data on-device. At the same time, a centralized risk engine aggregates signals from multiple sources to enable real-time decisioning and adaptive thresholding.
Traditional vs AI-Driven KYC Systems
| Dimension | Traditional KYC | AI-Driven KYC |
|---|---|---|
| Detection Logic | Rule-based | Multi-signal AI |
| Liveness Detection | Server-side only | Edge + Cloud |
| Latency | High | Optimized |
| Fraud Adaptability | Low | High |
| Scalability | Limited | High |
Next Steps for Engineering Teams
KYC fraud has evolved into an adversarial systems problem rather than a standalone model accuracy issue. Engineering teams must focus on reducing latency, moving computation closer to the user, integrating multi-signal risk scoring, and stress-testing systems against AI-generated fraud scenarios.
A practical next step is to benchmark current system performance, identify bottlenecks in both model inference and network transmission, and evaluate architectural upgrades that support edge deployment and real-time decisioning.
FAQ
What is driving the increase in KYC fraud?
The rapid advancement of AI-generated content, including deepfakes and synthetic identities, is the primary driver. These techniques allow attackers to bypass traditional verification systems that rely on static rules.
How does edge computing improve KYC systems?
Edge computing enables on-device processing, reducing latency and filtering fraudulent inputs before they reach the server. This improves both performance and security.
Why is multi-signal verification necessary?
Single-factor verification is vulnerable to spoofing. Multi-signal systems combine biometric, behavioral, and device data to improve detection accuracy.
Is gRPC necessary for KYC systems?
It is not mandatory, but it provides clear performance benefits in high-throughput scenarios by reducing payload size and enabling streaming.
How should teams measure KYC performance?
Key metrics include false acceptance rate, false rejection rate, end-to-end latency, and attack detection rate. Testing should include both real-world and adversarial scenarios.
Meta Description
KYC fraud in digital banking is evolving with AI-driven attacks such as deepfakes and synthetic identities. This technical guide explains system-level vulnerabilities and provides actionable solutions, including edge computing, model optimization, and multi-signal risk scoring to build a scalable, low-latency, and fraud-resistant KYC architecture.

